| Number of Risk Management Committee Meetings Held | |
|---|---|
| FY2024 | 6 |
| FY2023 | 4 |
| FY2022 | 4 |
Risk Management
Policy and Basic Approach
Strengthening the risk management system
The Gunze Group has established a Risk Management Committee to prevent risks in general and respond appropriately to unforeseen situations and contingencies.
With the goal of eliminating industrial accidents, misconduct, and all forms of harassment, we are identifying specific risks and working on measures to minimize
them.
Goals and Achievements
System
The Risk Management Committee deliberates and reviews matters concerning risk prevention, responses to risks that have occurred, and measures to prevent recurrence,
based on regulations governing risk management.
This committee consists of the Compliance Officer and department heads.
Risk Management Initiatives
The Risk Management Committee met six times in FY2024, during which it received monitoring result reports from the main departments designated to take charge of each of
these risks, verified the execution status of countermeasures, and discussed and determined future action.
These initiatives are reported to the Board of Directors, which issues instructions as necessary to ensure the effectiveness of internal controls.
Since FY2022, relevant functional departments have collaborated to conduct on-site audits at factories and business sites to prevent misconduct.
The Risk Management Committee also regularly shares audit results to drive further improvements. We are also working to strengthen our support system, taking into
account the risks faced by employees posted overseas.
In light of the succession of large-scale disasters and conflicts occurring both domestically and internationally in recent years, we are strengthening our response
framework by developing and reviewing internal regulations to enable swift and appropriate action during emergencies.
In FY2023, we placed particular emphasis on providing a safe working environment for employees, and with the eradication of industrial accidents in mind proceeded with
earthquake resistance inspections of each business location and the demolition of aging facilities.
As a responsibility of a manufacturer and seller of products, we must not only avoid any violations of the Act against Unjustifiable Premiums and Misleading
Representations or the Act on Securing Quality, Efficacy and Safety of Products Including Pharmaceuticals and Medical Devices (the Pharmaceutical and Medical Device
Act) but also the risk of causing inconvenience to customers through inappropriate language in products or advertisements.
In accordance with the increasing number of opportunities to provide apparel products by online sales in particular, it is becoming increasingly important to use labels
and expressions that are appropriate for as many people as possible.
We are working to minimize risk by having staff from multiple departments use an in-house database to check the labeling and expressions of products delivered to
customers in advance and by conducting in-house training.
The Risk Management Committee in fiscal 2022, during which it received monitoring result reports from the main departments designed to take charge of each of these
risks, verified the execution status of countermeasures, and discussed and determined future action.
In regard to the risks of row material price fluctuations and supply disruptions due to charges in international relations, the Risk Management Committee collects
information on and ascertains the risks faced by each business division, after which the head office and business division work in unison on risk management efforts.
Moreover, a risk has emerged regarding social credibility loss due to the increasing numbers of violations of the Act against Unjustifiable Premiums and Misleading
Representations and of the Pharmaceutical and Medical Device Act, as well as to the increasing frequency of inappropriate expressions, resulting from the apparel
business’s efforts to promote greater sales through e-commerce channels.
In regard to this risk, the Risk Management Committee will engage in activities that mitigate such risks across business divisions and that increase corporate value on
an ongoing basis, namely through training organized by Legal & Compliance and through internal database inspections conducted by representatives from multiple
divisions, for example.
Data Security and Privacy We will enhance security measures and competitiveness through strengthened governance and risk management tailored to the digital transformation era.
Security Policy In FY2006 the Gunze Group established an IT Security Policy, and has since engaged in systematic efforts to understand the risk status of the entire Group based on its organizational structure, formulate basic policies, conduct regular diagnostics and monitoring, respond to incidents, and improve security awareness.
IT Security Policy Overview
| Content | |
|---|---|
| 1. Basic Principles | This policy outlines fundamental matters, including ensuring the appropriateness, effectiveness, and efficiency of operations through information security regarding the use and protection of all information assets, and that this policy applies to all officers and employees. |
| 2. Organizational Structure | Outlines the organizational structure headed by the President and the operational framework centered on the IT Officer, along with their respective responsibilities |
| 3. Responsibilities of Officers and Employees | Compliance requirements for maintaining and enhancing IT information security, and handling of information assets |
| 4. Legal Compliance | Compliance with relevant laws and regulations (Personal Information Protection Act, Unauthorized Access Prohibition Act, Copyright Act, etc.) and norms |
| 5. Response to Incidents | In the event of an incident, an incident response team commensurate with the impact level shall be established and activated. Additionally, the incident response policy shall include collaborating with relevant departments to ensure timely and appropriate external disclosure, as well as reporting to authorities in each country and region. |
| 6. Response to Violations | Disciplinary actions for violations by officers and employees of the provisions set forth in these regulations and related documents |
System
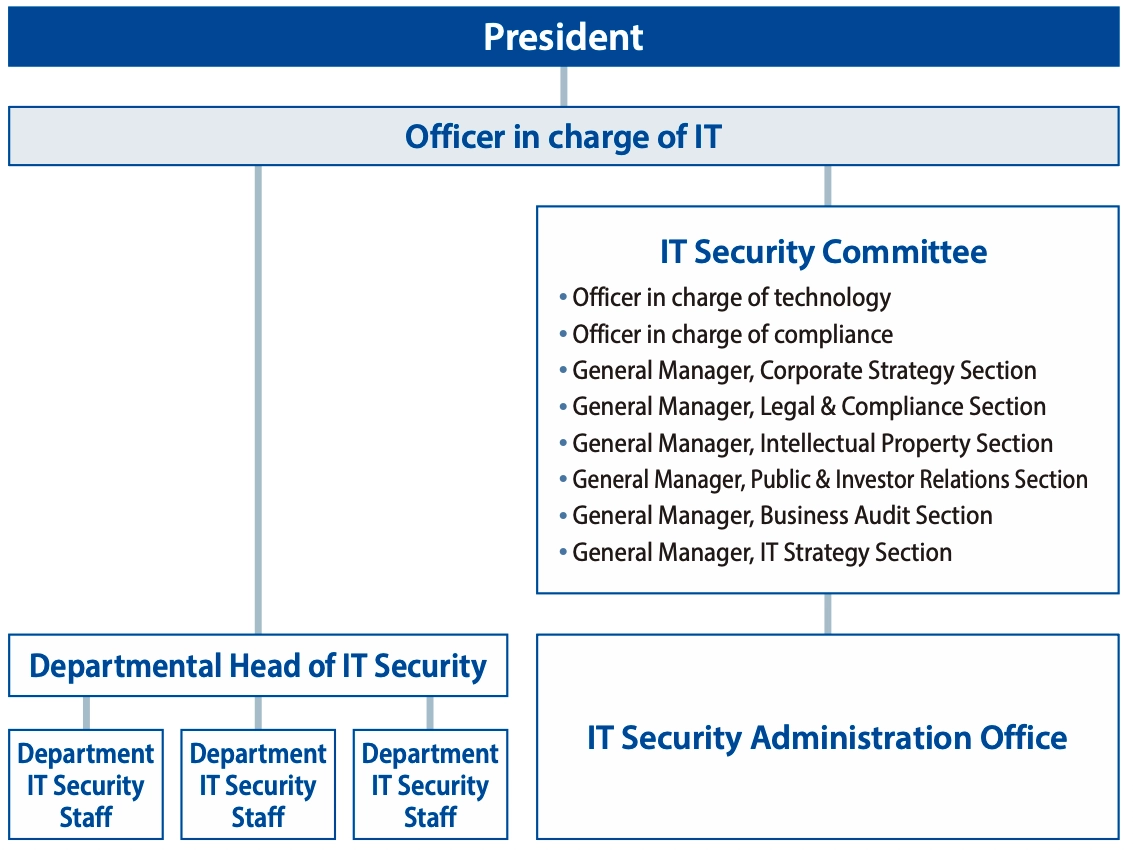
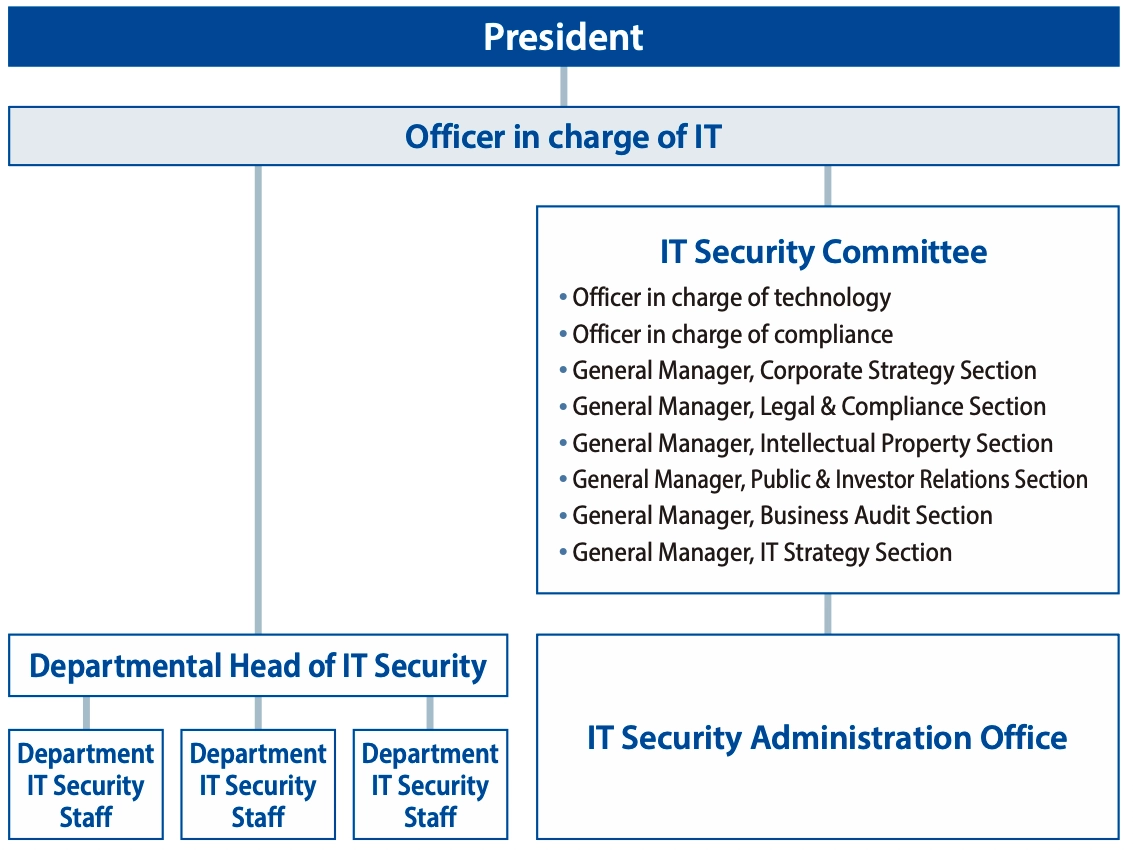
The Gunze Group has established an IT Security Committee, chaired by an IT officer appointed by management, as an organization to promote security
countermeasure activities.
This Committee as part of our system to promote cybersecurity, keep track of security-related situations, formulate countermeasure standards, maintain a
management system, and deliberate and decide on necessary measures.
In addition, we have established an IT Security Administration Office to implement and supervise the measures decided by the Committee, and instruct and follow
up with security officers and personnel in charge of each department on the status of security measures.
IT Security Operations Organizational Chart